Alma ADR vs. Zero-Day Exploits: Catching Exploitation Without a CVE

Research Team
Introduction
Zero day exploits are one of the scariest realities in cybersecurity. They strike without warning, bypassing signature based defenses because no CVE has been issued yet, and no patch exists. Traditionally, defenders only realize the danger once an exploit is already being traded on dark markets.
But what if your system could detect exploitation attempts in real time, even when the vulnerability has never been disclosed?
That’s exactly what happened when our ADR platform flagged a live zero day in Emby, a popular media streaming software used by millions worldwide.
The Exploit: IDOR in Emby
While analyzing Emby, we uncovered a classic Insecure Direct Object Reference (IDOR) vulnerability. The flaw allowed attackers to retrieve arbitrary user records simply by changing the resource ID in the request:
No robust authorization checks existed, meaning a valid session could be reused to access multiple user accounts. In practice, this enabled:
Exposure of sensitive user data (names, account details).
Account enumeration by iterating through user IDs.
Potential privilege escalation by harvesting privileged accounts.
In other words, a single weak endpoint placed millions of Emby users at risk.
How Alma’s ADR Flagged It Immediately
Unlike signature based security tools that would have missed this, ADR detected the anomaly in real time.
From the system logs:
Two separate
GET /emby/Users/<id>requests were issued with the same session token.Both requests returned 200 OK, each revealing details of different user accounts.
ADR immediately correlated this pattern as abnormal behavior. a single user session retrieving unrelated user objects.
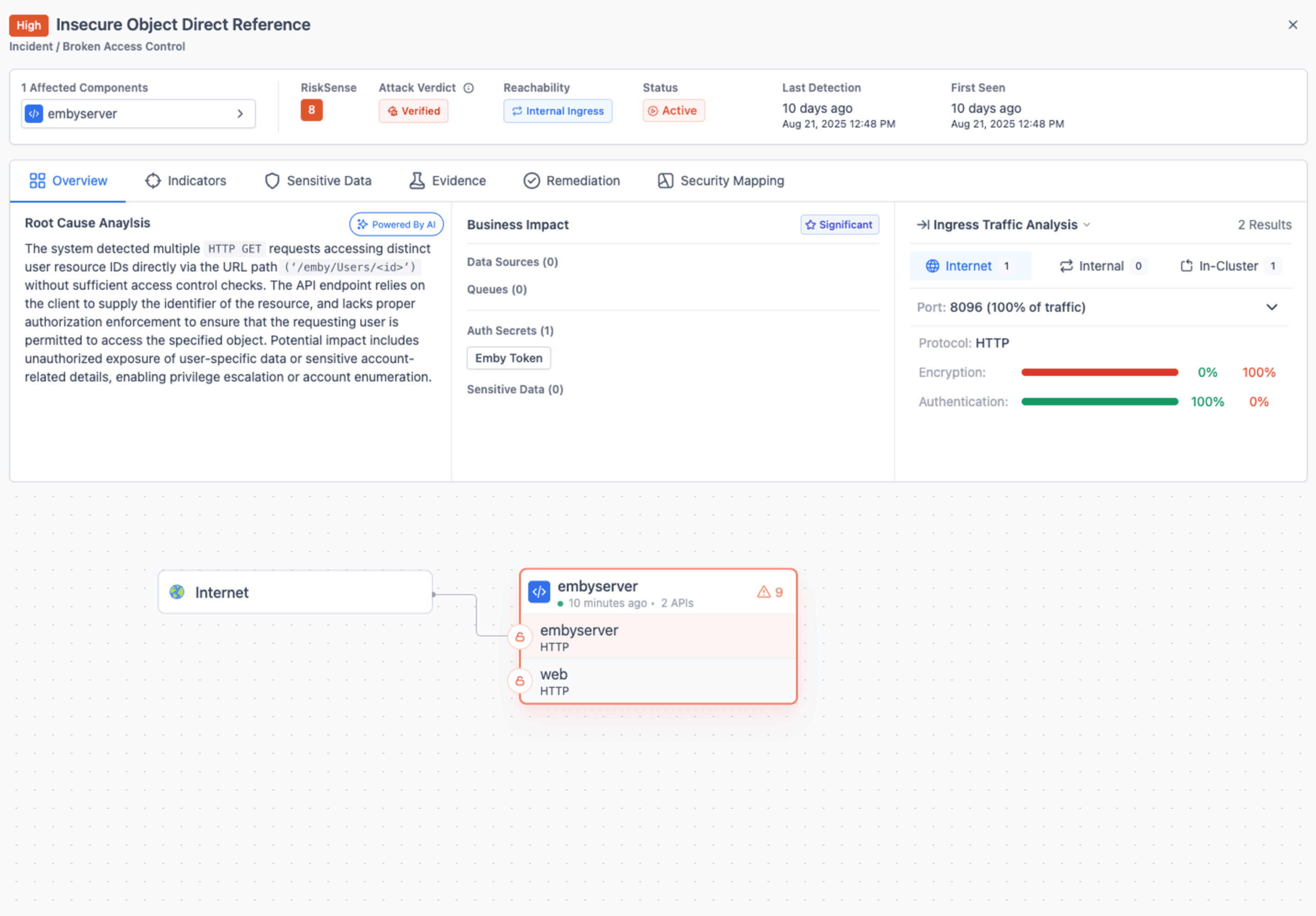
Alma’s Root Cause Analysis engine immediately generated the following finding:
“The system detected multiple HTTP GET requests accessing distinct user resource IDs directly via the URL path without sufficient access control checks. Potential impact includes unauthorized exposure of user specific data, enabling privilege escalation or account enumeration.”
IOC and Attack Footprint
To make the detection actionable, Alma’s ADR attached the full attack footprint and indicators of compromise (IOC):
Session Token Reuse:
b144442f153e4152b887fc6278ac8770Exploit Requests:
GET /emby/Users/62d9b52297384a23a93383d4ab5a9beaGET /emby/Users/5f488ee2d4ba4814a5211b11148fd8a3
Exposed Data:
Name: User1Name: User3


This footprint gave security teams immediate visibility not just that an attack happened, but who was impacted, how it was exploited, and what token was used.
Remediation Steps: From Detection to Defense
ADR doesn’t just stop at detection and incident generation. it also provides clear, actionable remediation guidance so development and security teams know exactly how to fix the underlying issue. For the Emby IDOR case, the system recommended several best practice countermeasures, mapped to OWASP guidelines:

By embedding these steps directly into the incident view, ADR shortens the gap between detection and resolution. Instead of leaving teams with vague alerts, it provides a roadmap for securing the application against similar zero day exploitation attempts in the future.
Why This Matters
No CVE Needed: ADR caught the exploit on behavior alone, not by waiting for a signature or advisory.
Instant Correlation: Multiple suspicious requests tied together under a single incident, preventing alert fatigue.
Attack Verdict: ADR automatically highlighted the exact session token, user IDs, and HTTP responses that triggered the incident, giving investigators immediate clarity and a direct path to validation.
Actionable Output: IOC + contextual root cause analysis meant remediation could start immediately.
Protection Before Patch: Even if Emby users weren’t patched yet, they could detect and block exploitation in real time.
Bigger Picture: ADR as a Zero Day Radar
This case demonstrates the true value of ADR. Attackers don’t wait for CVEs, and neither should defenders. By focusing on application layer behavior, telemetry correlation, and anomaly detection, ADR offers a new way forward:
Detecting misuse of authentication tokens
Spotting cross user access attempts
Exposing unexpected data access patterns
Instead of chasing the patch cycle, ADR shifts detection left into the attack itself.
From Detection to Disclosure: Six CVEs Assigned
What began as real time testing of ADR’s capabilities grew into a full vulnerability investigation. The findings were responsibly reported to the Israeli National Cyber Directorate (INCD), and after validation, resulted in the publication of six separate CVEs affecting Emby MediaBrowser version 4.9.0.35.
Each CVE highlighted a different aspect of improper access control and authorization flaws:
CVE-2025-46391 – CWE-284: Improper Access Control
CVE-2025-46390 – CWE-204: Observable Response Discrepancy
CVE-2025-46389 – CWE-620: Unverified Password Change
CVE-2025-46388 – CWE-200: Exposure of Sensitive Information to an Unauthorized Actor
CVE-2025-46387 – CWE-639: Authorization Bypass Through User-Controlled Key
CVE-2025-46386 – CWE-639: Authorization Bypass Through User-Controlled Key
All six issues were disclosed on July 20, 2025, with the highest severity rating assigned a CVSS score of 8.8 (High).

This disclosure illustrates the full lifecycle of ADR’s value: not just detecting exploitation attempts in the wild, but enabling responsible reporting that contributes back to the global security community and helps protect millions of users.
Conclusion
The Emby zero day IDOR highlights a broader truth: zero day exploits will continue to surface, and defenders must be ready. With ADR, organizations aren’t blind while waiting for CVEs or patches. They can see exploitation in motion, understand the footprint, and respond immediately.
For Emby users, this was a warning. For ADR, it was validation.
Catching a zero day before it became a headline.